Featured
Table of Contents
Vpn Troubleshooting Guide (2023)
The Routing and Remote Gain access to snap-in lives within the Microsoft Management Console, called the MMC. There are several methods to access the MMC. You can select the console from the Start menu's Programs choices, within the Administrative Tools folder within Windows server's Control board or by typing mmc at a command prompt.
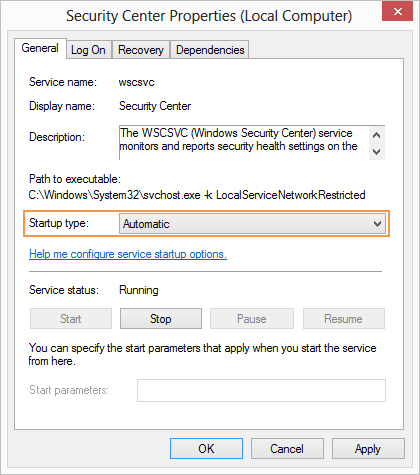
As Tech, Republic's Brandon Vigliarolo demonstrates within his video at the start of this post, the Services console displays the status of the Routing and Remote Gain access to entry. From within the Solutions console and with the Routing and Remote Gain access to entry highlighted, you can click Start the Service or right-click the entry and select Restart.
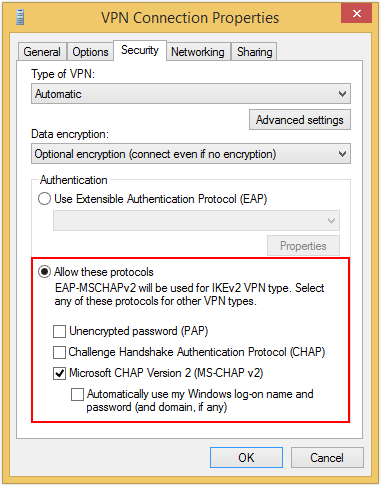
Often the VPN client and VPN server are set to using different authentication methods. Verify whether an authentication mistake is the problem by opening the server console. Another technique of accessing the MMC is to type Control+R to open a command timely in which you can type mmc and struck Enter or click OK.
If the entry isn't present, click File, choose Add/Remove Snap-in, pick the Routing and Remote Gain access to alternative from the options and click Include, then OK. With the Routing and Remote Access snap-in included, right-click on the VPN server and click Characteristics. Then, review the Security tab to validate the authentication technique.
Anyconnect Vpn Client Troubleshooting Guide
Make sure the VPN client is set to the authentication method specified within the Security tab. Usually the items simply reviewed are accountable for many VPN connection rejection errors. Other basics need to be proper, too. For example, if the Windows Server hosting the VPN hasn't joined the Windows domain, the server will be unable to confirm logins.
IP addresses are another essential element for which administration should be correctly set. Each Web-based VPN connection usually uses 2 different IP addresses for the VPN client computer system. The first IP address is the one that was designated by the client's ISP. This is the IP address that's utilized to develop the preliminary TCP/IP connection to the VPN server over the Internet.

This IP address typically possesses the very same subnet as the local network and hence enables the client to interact with the regional network. When you established the VPN server, you must configure a DHCP server to appoint addresses to clients, or you can create a bank of IP addresses to designate to customers directly from the VPN server.

If this option is selected and the effective remote gain access to policy is set to allow remote gain access to, the user will be able to attach to the VPN. Although I have actually been unable to re-create the circumstance personally, I have heard rumors that a bug exists in older Windows servers that can cause the connection to be accepted even if the effective remote access policy is set to deny a user's connection.
Troubleshoot Knox Issues - Samsung Knox Workspace
Another common VPN problem is that a connection is successfully developed but the remote user is unable to access the network beyond the VPN server. Without a doubt, the most common cause of this problem is that approval hasn't been given for the user to access the whole network. To allow a user to access the whole network, go to the Routing and Remote Access console and right-click on the VPN server that's having the problem.
At the top of the IP tab is an Enable IP Routing check box. If this check box is enabled, VPN users will have the ability to access the remainder of the network, presuming network firewall programs and security-as-a-service settings permit. If the checkbox is not picked, these users will be able to access only the VPN server, however nothing beyond.
If a user is dialing directly into the VPN server, it's generally best to configure a fixed route in between the customer and the server. You can configure a static path by going to the Dial In tab of the user's homes sheet in Active Directory Users and Computers and picking the Apply A Fixed Route check box.
Click the Include Route button and after that go into the destination IP address and network mask in the area supplied. The metric should be left at 1. If you're utilizing a DHCP server to appoint IP addresses to customers, there are a couple of other issues that could trigger users not to be able to surpass the VPN server.
The Vpn Tunnel Goes Down Frequently. - Fortigate / Fortios ...
If the DHCP server appoints the user an IP address that is currently in use somewhere else on the network, Windows will find the dispute and prevent the user from accessing the rest of the network. Another typical issue is the user not receiving an address at all. Most of the time, if the DHCP server can't appoint the user an IP address, the connection won't make it this far.
If the client is appointed an address in a range that's not present within the system's routing tables, the user will be not able to browse the network beyond the VPN server. Ensure the resources the user is trying to gain access to are really on the network to which the user is connecting.
A VPN connection to the other subnet might, in reality, be needed. A firewall program or security as a service solution might also be to blame, so don't forget to review those options' settings, if such parts are present between the VPN server and the resources the user seeks to reach.
The very first possibility is that one or more of the routers included is performing IP packet filtering. IP package filtering could avoid IP tunnel traffic. I advise checking the customer, the server and any makers in between for IP package filters. You can do this by clicking the Advanced button on each maker's TCP/IP Characteristics sheet, choosing the Options tab from the Advanced TCP/IP Settings Characteristic sheet, choosing TCP/IP Filtering and clicking the Properties button.
Latest Posts
Best Vpn For Business
9 Best Corporate & Small Business Vpn Solutions
Vpn By Google One - Extra Online Security For Your Phone