Featured
Table of Contents
Why Your Vpn Keeps Disconnecting And How To Prevent It
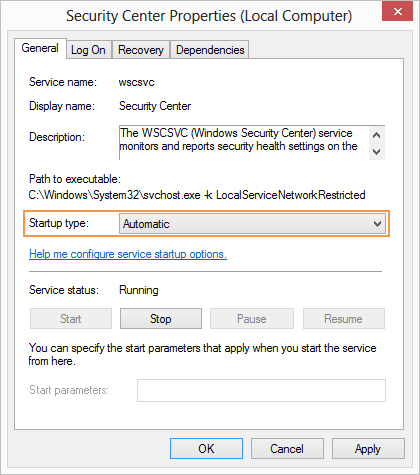
The Routing and Remote Gain access to snap-in lives within the Microsoft Management Console, referred to as the MMC. There are several ways to access the MMC. You can pick the console from the Start menu's Programs options, within the Administrative Tools folder within Windows server's Control Panel or by typing mmc at a command prompt.
As Tech, Republic's Brandon Vigliarolo shows within his video at the start of this post, the Services console shows the status of the Routing and Remote Gain access to entry. From within the Services console and with the Routing and Remote Access entry highlighted, you can click Start the Service or right-click the entry and choose Restart.
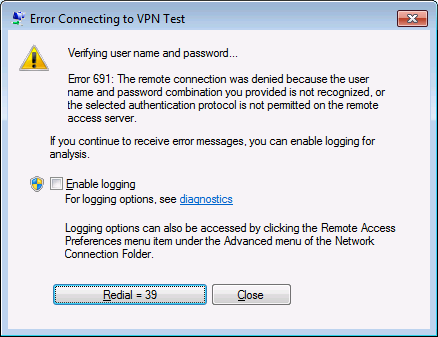
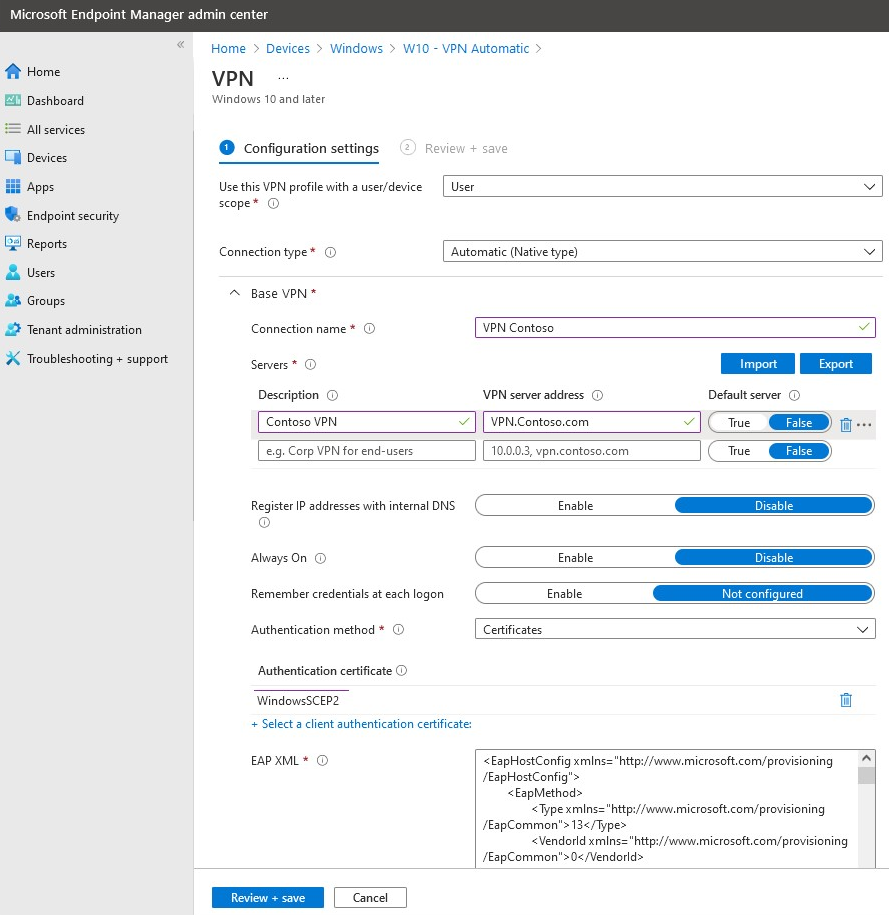
In some cases the VPN customer and VPN server are set to utilizing different authentication techniques. Verify whether an authentication mistake is the issue by opening the server console. Yet another approach of accessing the MMC is to type Control+R to open a command prompt in which you can type mmc and struck Enter or click OK.
If the entry isn't present, click File, choose Add/Remove Snap-in, choose the Routing and Remote Access alternative from the choices and click Include, then OK. With the Routing and Remote Access snap-in added, right-click on the VPN server and click Residences. Examine the Security tab to verify the authentication method.
Top Ngfw Troubleshooting Articles
Make sure the VPN client is set to the authentication technique defined within the Security tab. Generally the products simply evaluated are accountable for most VPN connection rejection errors. But other basics should be appropriate, too. For example, if the Windows Server hosting the VPN hasn't signed up with the Windows domain, the server will be unable to validate logins.
Each Web-based VPN connection normally uses two different IP addresses for the VPN client computer. This is the IP address that's utilized to develop the initial TCP/IP connection to the VPN server over the Web.
This IP address typically has the very same subnet as the local network and hence allows the client to interact with the local network. When you set up the VPN server, you must configure a DHCP server to assign addresses to customers, or you can produce a bank of IP addresses to designate to customers straight from the VPN server.

If this choice is chosen and the reliable remote gain access to policy is set to permit remote access, the user will have the ability to connect to the VPN. I have actually been not able to re-create the situation personally, I have heard rumors that a bug exists in older Windows servers that can cause the connection to be accepted even if the effective remote access policy is set to reject a user's connection.
Troubleshoot The Genesys Cloud Webrtc Phone
Another typical VPN issue is that a connection is successfully developed however the remote user is unable to access the network beyond the VPN server. Without a doubt, the most common cause of this problem is that authorization hasn't been granted for the user to access the whole network. To enable a user to access the whole network, go to the Routing and Remote Gain access to console and right-click on the VPN server that's having the problem.
At the top of the IP tab is an Enable IP Routing check box. If this check box is made it possible for, VPN users will have the ability to access the remainder of the network, assuming network firewall softwares and security-as-a-service settings permit. If the checkbox is not selected, these users will have the ability to access just the VPN server, but absolutely nothing beyond.
If a user is calling straight into the VPN server, it's generally best to configure a static path between the client and the server. You can set up a static path by going to the Dial In tab of the user's residential or commercial properties sheet in Active Directory Users and Computers and selecting the Apply A Fixed Path check box.
Click the Include Route button and after that get in the location IP address and network mask in the area supplied. The metric ought to be left at 1. If you're using a DHCP server to assign IP addresses to clients, there are a number of other issues that could trigger users not to be able to exceed the VPN server.
5 Common Vpn Issues And Solutions To Fixing Them
If the DHCP server assigns the user an IP address that is already in usage in other places on the network, Windows will discover the conflict and avoid the user from accessing the remainder of the network. Another typical problem is the user not getting an address at all. Many of the time, if the DHCP server can't designate the user an IP address, the connection won't make it this far.
254.x. x range. If the customer is assigned an address in a variety that's not present within the system's routing tables, the user will be not able to browse the network beyond the VPN server. Other problems can contribute to this issue, too. Ensure the resources the user is trying to gain access to are really on the network to which the user is connecting.
A VPN connection to the other subnet might, in reality, be needed. A firewall software or security as a service solution could also be to blame, so do not forget to evaluate those solutions' settings, if such parts exist in between the VPN server and the resources the user seeks to reach.
The first possibility is that one or more of the routers included is carrying out IP packet filtering. I suggest examining the customer, the server and any makers in between for IP package filters.
Latest Posts
Best Vpn For Business
9 Best Corporate & Small Business Vpn Solutions
Vpn By Google One - Extra Online Security For Your Phone